What is a penetration test?
A penetration test or “pen test” is a simulated attack on an information system authorized by the requester to evaluate the security of one’s target. A pen tester’s goal is to provide information to the company about their vulnerabilities. In the world of security this is commonly referred to as red teaming. On the other side of penetration testing the company’s security team, the blue team, figure out what areas of their security need to be strengthened. One can test many things: network, application (web and mobile), cloud and even humans.
Hacker vs Researcher
A pen tester is different from a malicious hacker because of permission and reporting. The pen tester must follow a scope given by the company that could be a domain, a network, a specific application, etc. and is given permission to try harmful techniques in order to hack the system. In the end, every vulnerability they found must be recorded and reported to the company.
Penetration test steps
No matter what type of target is tested, every pen test shares the same methodology:
- Scanning and Information gathering: Retrieve information about the target using public sources or by scanning the systems and applications.
- Vulnerability analysis and Threat modelling: With the result of information gathering, list all discovered vulnerability and draw a map of potential security holes and attack vector.
- Exploitation: Exploit a known vulnerability in order to gain access to the system.
- Reporting: Describe all vulnerability and detail impact on the company.

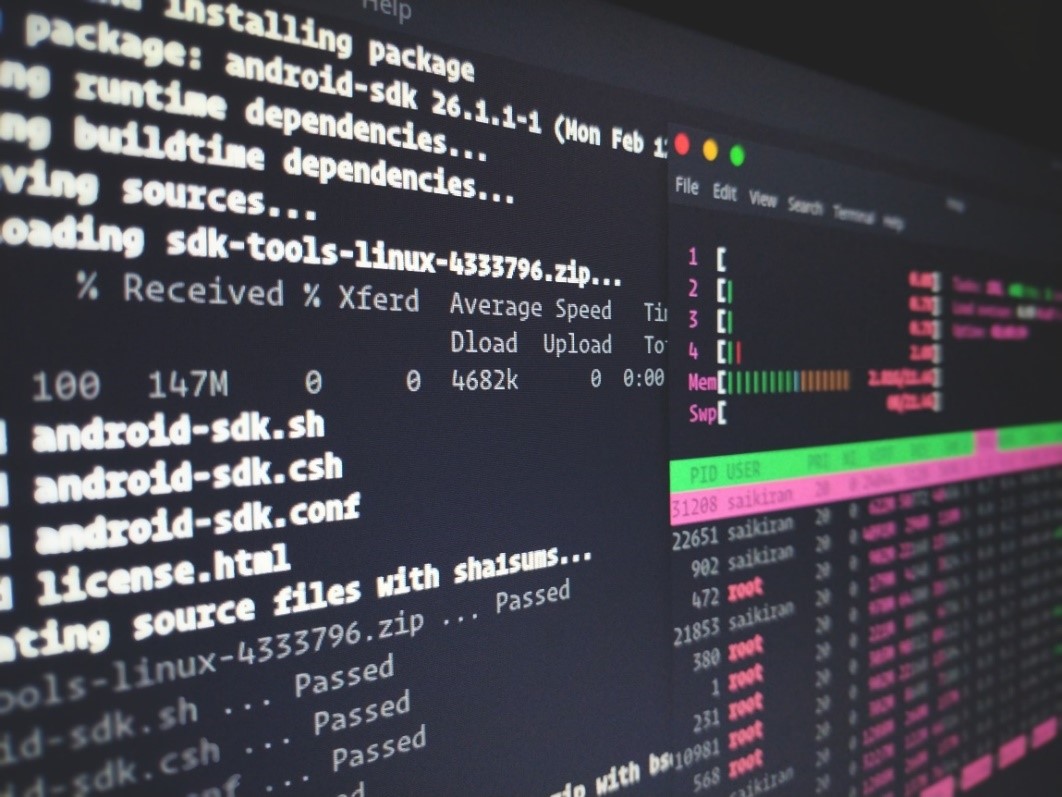
The pen tester’s environment
Security-focused operating system, vulnerability scanner, credentials brute force tool, etc… Numerous tools are available to help the pen tester on performing the security assessment on the information system. One of most known tools is the operating system: Kali Linux. It contains many useful tools and scripts for a pen tester as well as a complete environment to work efficiently. Nevertheless, a pen tester’s main weapon is his creativity because he must get into the mind of a malicious hacker.
Bug Bounty or the public penetration testing platform
In the world of penetration testing, a new trend is growing among companies: Bug bounty platforms. It consists of a list of companies allowing everyone to test the security of their systems and rewarding security researchers depending on the criticality of the vulnerability. It’s a win-win situation where companies improve their security and hackers gain money and reputation. Many platforms already exist like  and YesWeHack for Europe. For example, on 8th August, Apple announce that they expand their bug bounty program to macOS and raises the maximum reward to $1 million.
Penetration testing at La Redoute
For the case of La Redoute, penetration testing has already been done and many others are coming. The goal is to continuously test the security of the information system and all the critical application in the company. Furthermore, every penetration test is followed and will be renewed to ensure that no more vulnerability is brought by the fix or discovered later.
Now that the introduction is done, the next step is to dive into the technical part. The next article of this series will be about scanning and information gathering.
[1] Source : Wired – Apple Gives Hackers a Special iPhone—And a Bigger Bug Bounty

